Sentinel connects to everything.
Out of the box.
No custom development. No integration projects. Sentinel ships with ready-to-activate connectors across every layer of your enterprise stack - cloud, observability, security, collaboration, and custom systems.
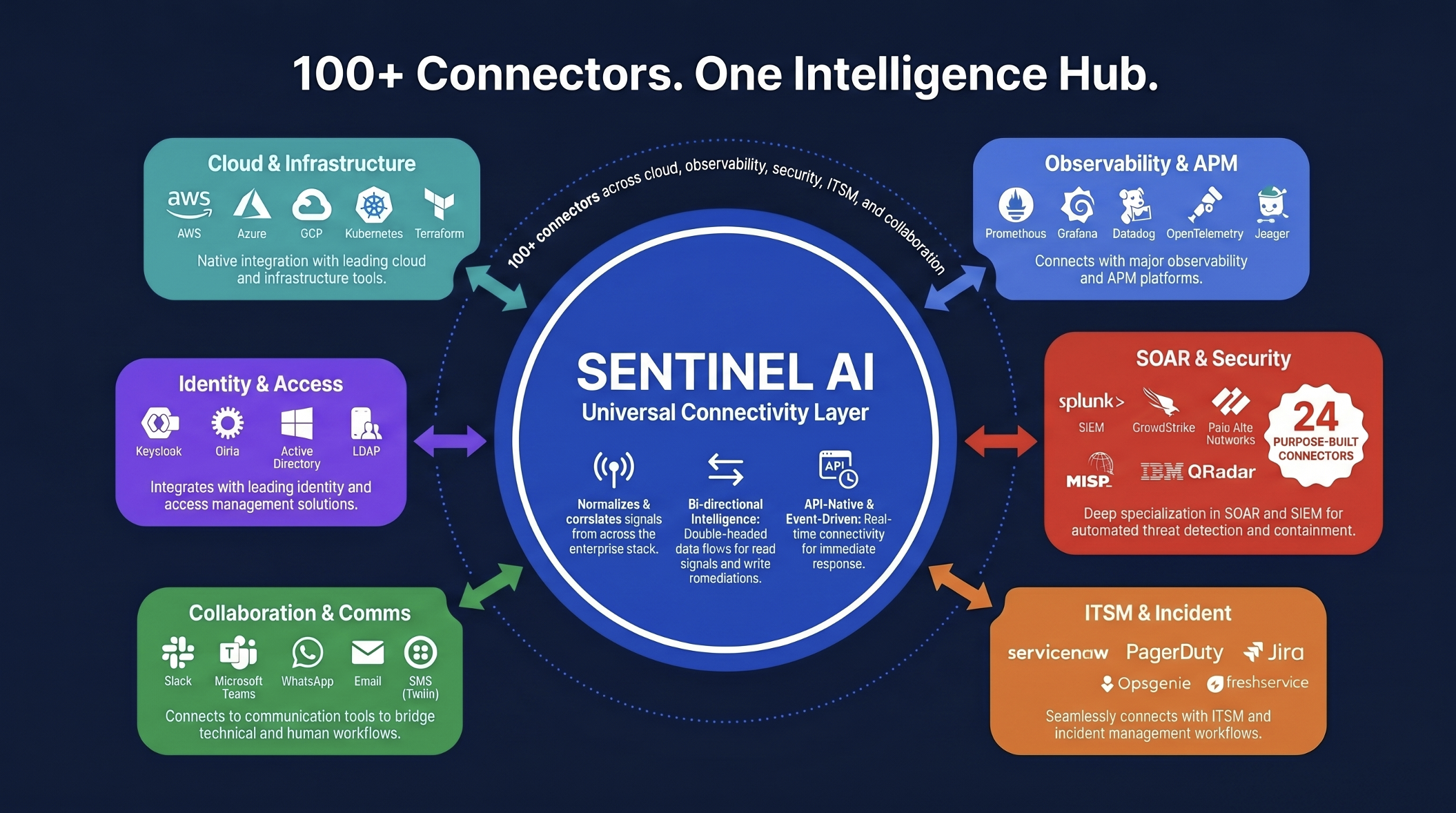
Bi-directional, event-driven connectors across cloud, observability, security, ITSM, and collaboration - including 24 purpose-built SOAR connectors for SecOps.