Unified MOP Library - Investigation & Execution
ProcBot is the single source of truth for all procedures. Investigation MOPs guide Sentinel's diagnostic reasoning when facing unknown failures. Execution MOPs are the step-by-step remediation scripts Sentinel runs to fix them. Both types stored, versioned, and continuously improved by Sherlock.
Ansible + Shell/Bash Execution Engine
ProcBot natively executes Ansible playbooks and shell/bash scripts - your existing automation library, unchanged. Bring your current runbooks: ProcBot wraps them with observability, audit logging, conditional branching, and rollback logic. Nothing rewritten, everything enhanced.
Human-in-the-Loop Approvals
For high-impact procedures, ProcBot triggers a human approval step. Sentinel presents the procedure, the evidence, and the risk assessment - and waits for confirmation before executing. Approval, action, and evidence are all audit-logged for compliance.
Escalation & Conditional Branching
Procedures aren't linear scripts - they're intelligent workflows. ProcBot supports conditional branching (if disk > 90% and service is critical, execute escalation path), timeout-based fallback, and multi-step approval chains. Every edge case handled, every action logged.
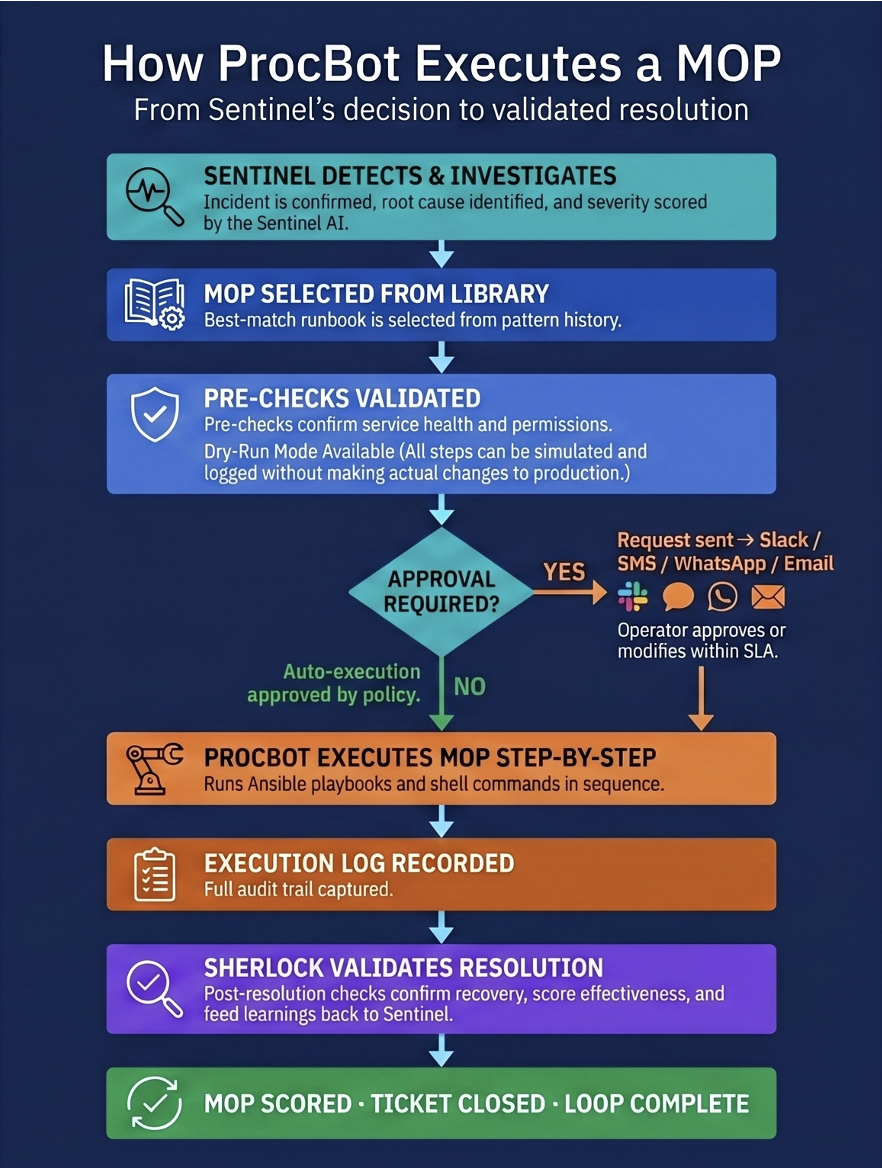
Every MOP step is logged, auditable, and scored by Sherlock - creating a continuously improving, self-optimising procedure library.