One Unified Intelligence.
Every pillar is purpose-built for its domain - and every pillar feeds Sentinel AI, the intelligence layer that connects them all.
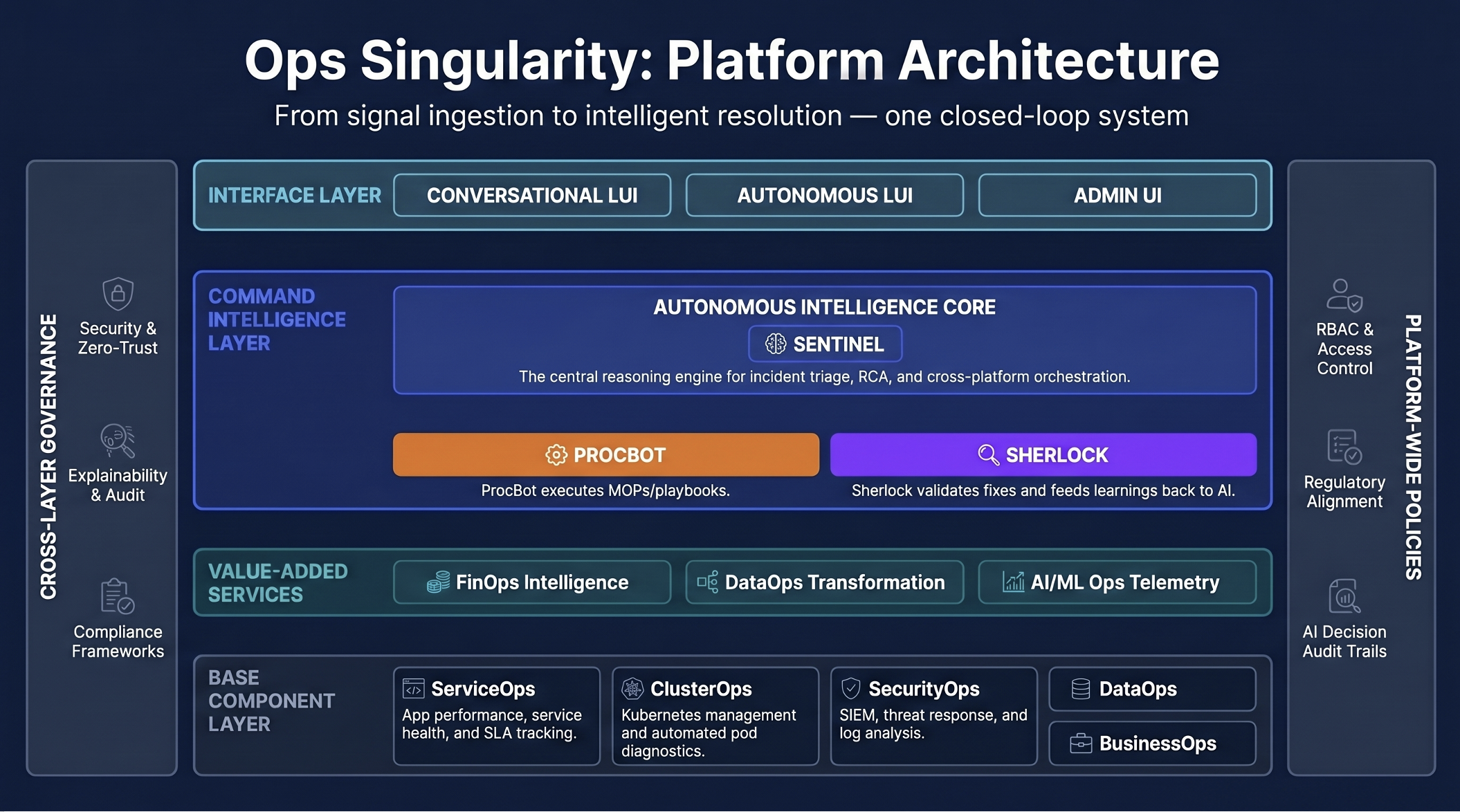
From six signal-source pillars through Sentinel AI's intelligence layer to every operator-facing interface - one continuous loop.